A North Korean hacking group is targeting crypto workers with a Python-based malware disguised as part of a fake job application process, researchers at Cisco Talos said earlier this week.
Most victims appear to be based in India, according to open-source signals, and seem to be individuals with prior experience in blockchain and cryptocurrency startups.
While Cisco reports no evidence of internal compromise, the broader risk remains clear: That these efforts are trying to gain access to the companies these individuals might eventually join.
The malware, called PylangGhost, is a new variant of the previously documented GolangGhost remote access trojan (RAT), and shares most of the same features — just rewritten in Python to better target Windows systems.
Mac users continue to be affected by the Golang version, while Linux systems appear to be unaffected. The threat actor behind the campaign, known as Famous Chollima, has been active since mid-2024 and is believed to be a DPRK-aligned group.
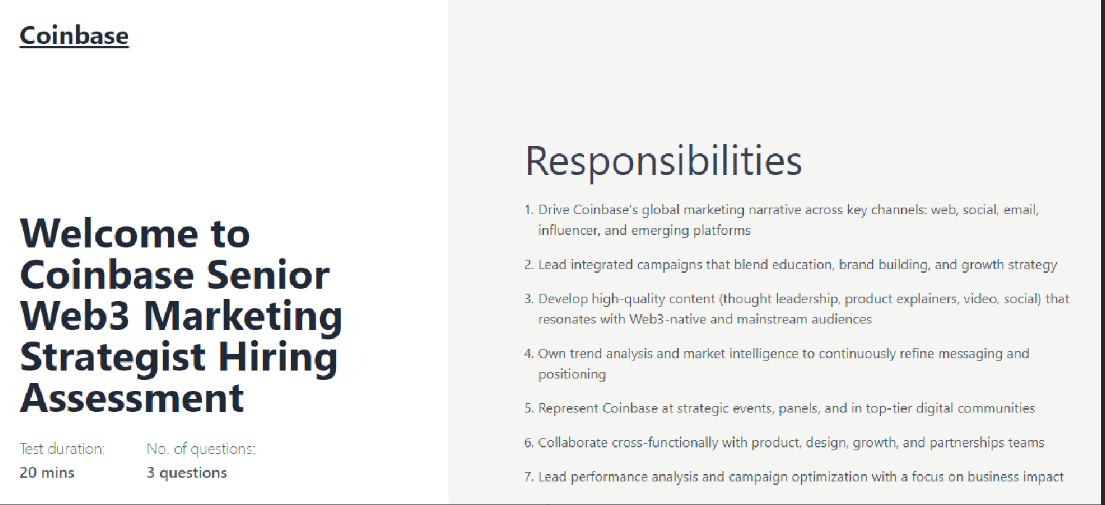
Their latest attack vector is simple: impersonate top crypto firms like Coinbase, Robinhood, and Uniswap through highly polished fake career sites, and lure software engineers, marketers, and designers into completing staged “skill tests.”
Once a target fills in basic information and answers technical questions, they’re prompted to install fake video drivers by pasting a command into their terminal, which quietly downloads and launches the Python-based RAT.
The payload is hidden in a ZIP file that includes the renamed Python interpreter (nvidia.py), a Visual Basic script to unpack the archive, and six core modules responsible for persistence, system fingerprinting, file transfer, remote shell access, and browser data theft.
The RAT pulls login credentials, session cookies, and wallet data from over 80 extensions, including MetaMask, Phantom, TronLink, and 1Password.
The command set allows full remote control of infected machines, including file uploads, downloads, system recon, and launching a shell — all routed through RC4-encrypted HTTP packets.
RC4-encrypted HTTP packets are data sent over the internet that are scrambled using an outdated encryption method called RC4. Even though the connection itself isn’t secure (HTTP), the data inside is encrypted, but not very well, since RC4 is outdated and easily broken by today’s standards.
Despite being a rewrite, the structure and naming conventions of PylangGhost mirror those of GolangGhost almost exactly, suggesting both were likely authored by the same operator, Cisco said.
Read more: North Korean Hackers Targeting Crypto Developers With U.S. Shell Firms

